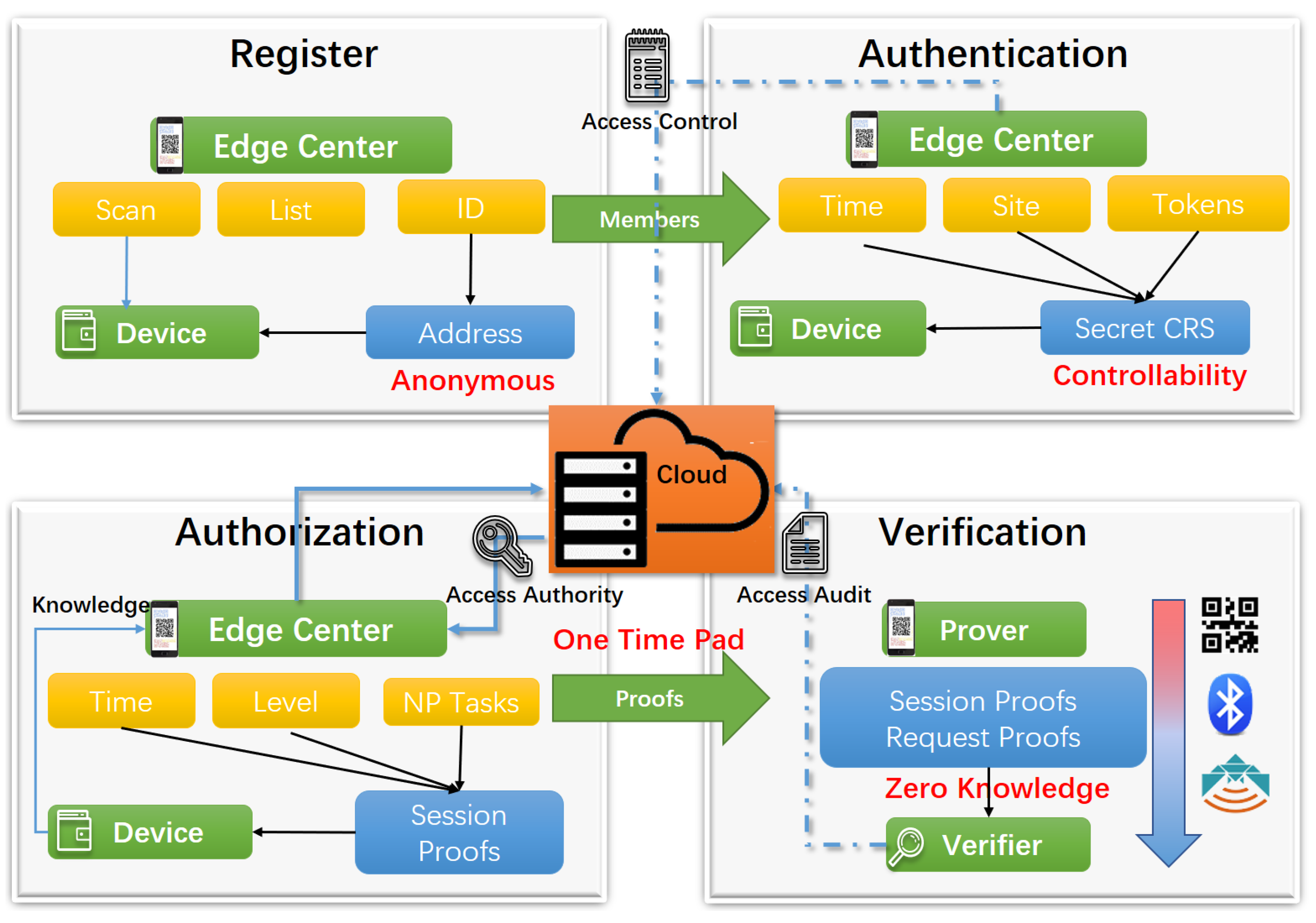
Sensors | Free Full-Text | Trustworthiness and a Zero Leakage OTMP-P2L Scheme Based on NP Problems for Edge Security Access

internet - Participating in my first every Hackathon And this is the speed test result ( more than 1000 participants are here ) - devRant

JCM | Free Full-Text | In Vivo Foot Segmental Motion and Coupling Analysis during Midterm Follow-Up after the Open Reduction Internal Fixation of Trimalleolar Fractures

zkChain: A privacy‐preserving model based on zk‐SNARKs and hash chain for efficient transfer of assets - Huang - Transactions on Emerging Telecommunications Technologies - Wiley Online Library

Time‐bound key‐aggregate encryption for cloud storage - Lee - 2016 - Security and Communication Networks - Wiley Online Library
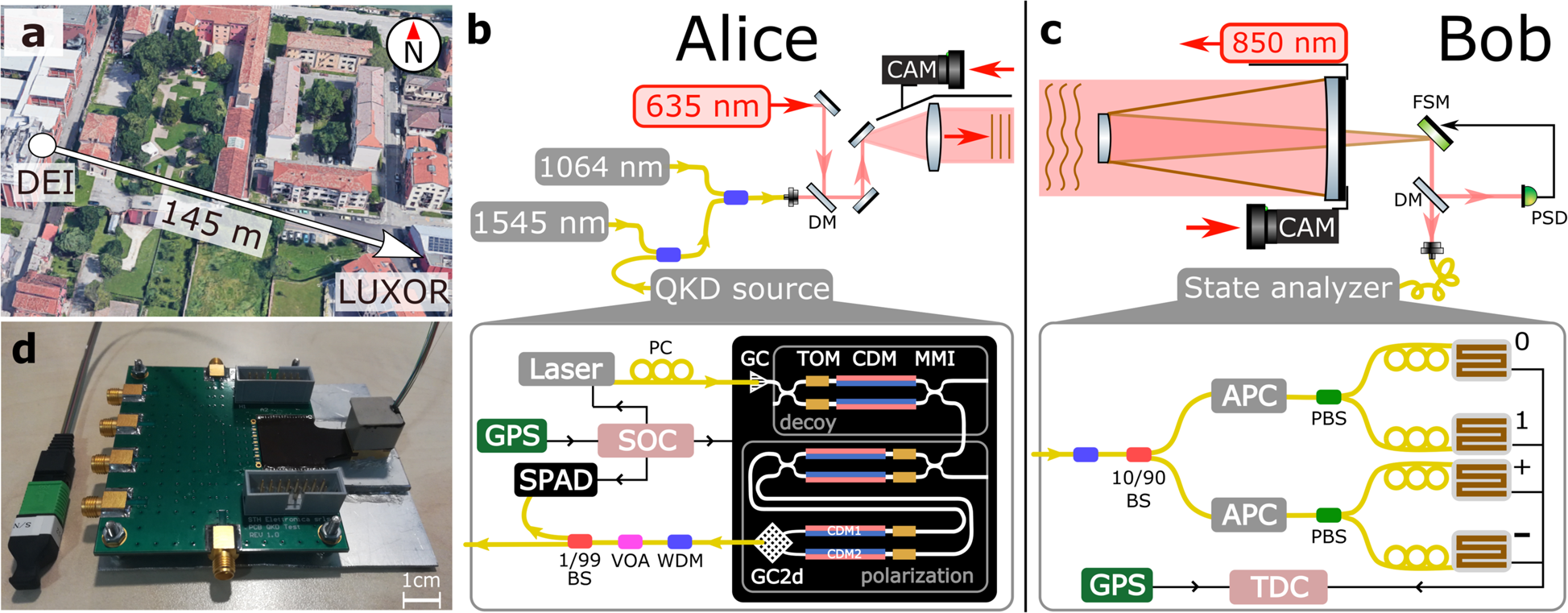
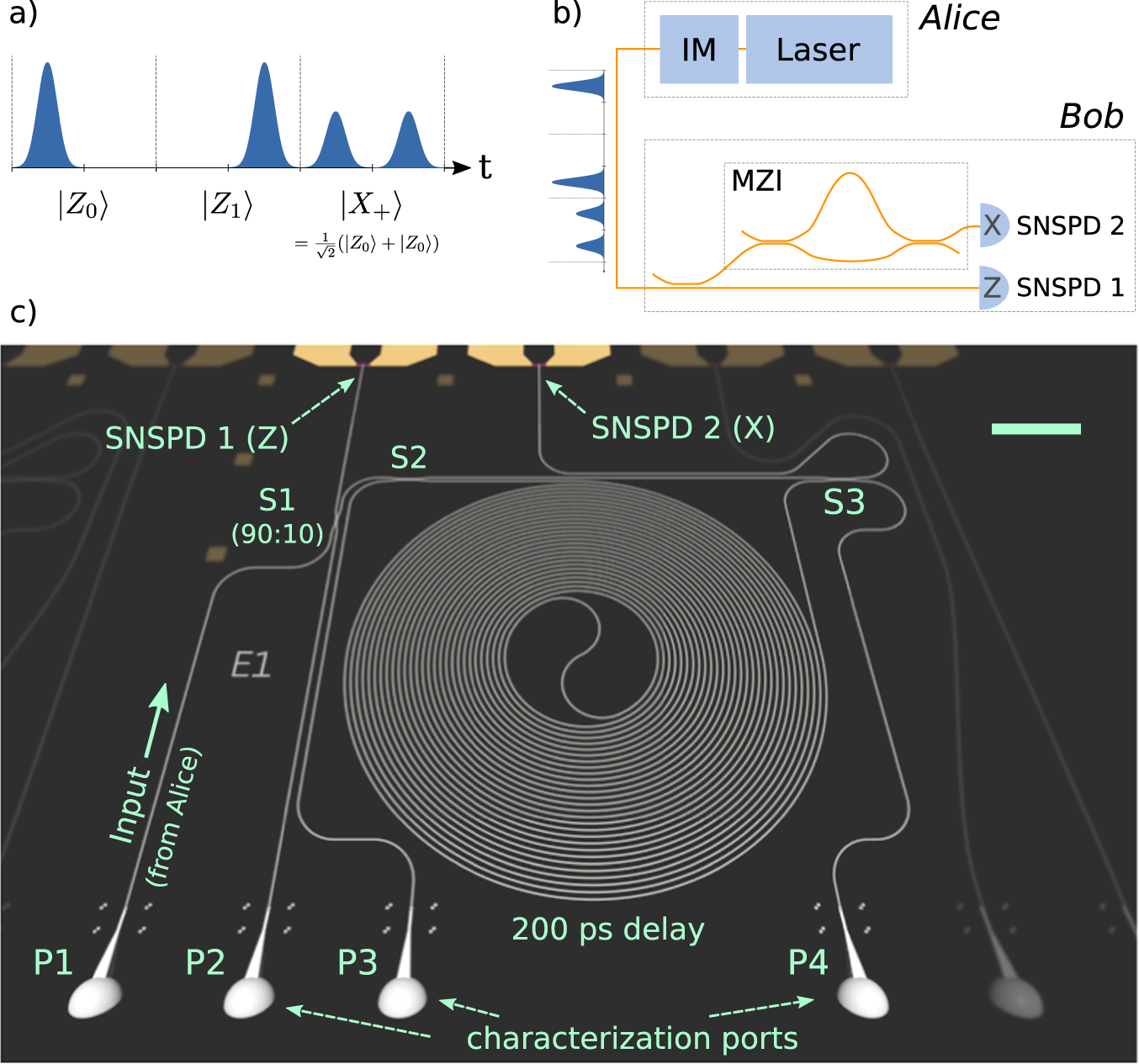
Full daylight quantum-key-distribution at 1550 nm enabled by integrated silicon photonics | npj Quantum Information